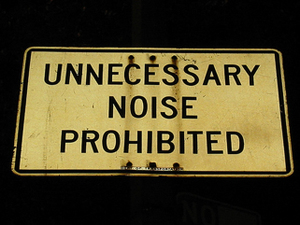
The sign owner dislikes needless racket. Nature abhors a vacuum. The law hates superfluity.
The Federal Circuit today held that a patentholder didn’t release future patent infringement claims despite release language that . . . released future patent infringement claims. The saving grace? That the parties’ lawyers, while drafting a settlement agreement that resolved patent litigation in New Jersey and another one relating to a patent case in Massachusetts, forgot to conform the two instruments so that both limited releases to claims that "were or could have been asserted" in the pending lawsuits.
Actually, that grace didn’t quite save the patentholder. The "were or could have been asserted", the court noted, seems to cover any claim that existed at the time of the settlements — a group that included the patent infringement claim at issue in the case before the court. So the court looked to extrinsic evidence to determine the parties’ intent and concluded that they meant the releases (a) to say the same thing and (b) to cover only the then-pending New Jersey and Massachusetts claims. Howmedica Osteonics Corp. v. Wright Medical Technology, Inc., No. 07-1363 (Fed. Cir. Sept. 2, 2008).
Blawgletter wonders at the court’s stretch. We could go along with the confusion about two simultaneous settlement agreements between the same parties — although we don’t feel as much sympathy for the lawyers who didn’t double-check the final versions before letting their clients sign them. But we marvel at the court’s treatment of the limitation of the releases to claims that "were or could have been asserted" in the pending cases. It doesn’t seem ambiguous to us. Nor does it, to us, imply a further restriction to the claims already before the New Jersey and Massachusetts courts. That construction renders the words, er, superfluous.